.webp)
Advisory & Compliance
Align your company’s security program with industry standards.
Strategic Risk Management Aligned to Your Business
At Access Point Consulting, our Advisory & Compliance practice goes beyond compliance checklists, integrating the best practices to manage risk with your business objectives. Our team of security experts works with you to establish a proactive, business-aligned approach that supports regulatory needs while minimizing operational and strategic risks.
We work hands-on with your organization to understand its unique security needs, compliance requirements, and risk tolerance. By combining deep cybersecurity expertise with strategic insights, we implement programs that not only protect your critical assets but also enhance your overall business resilience and agility.
Services

Virtual CISO
Access Point's Virtual Chief Information Security Officer (Virtual CISO) services empower organizations of all sizes with expert cybersecurity guidance and leadership, without the need for a full-time CISO. Our Virtual CISOs become an integral part of your leadership team, aligning cybersecurity efforts with your business objectives and risk tolerance.

Governance, Risk & Compliance
Access Point Consulting’s Governance, Risk, and Compliance (GRC) services simplify meeting complex regulatory demands such as HIPAA, PCI-DSS, and NYDFS, removing uncertainty from your compliance efforts. The service streamlines governance and risk management processes, safeguarding your organization from penalties, disruption, and loss of customer trust.

AI Readiness & Governance
Access Point Consulting’s AI Readiness and Governance service positions your organization to securely and effectively leverage artificial intelligence, including powerful generative AI technologies such as large-language models (LLMs). Our tailored governance framework aligns AI compliance with your particular business environment, enabling you to safely capitalize on AI's transformative potential.

Security Engineering
Access Point’s Security Engineering service provides a variety of security services—from network segmentation to identity management—that evolve with your compliance needs. Our comprehensive frameworks proactively address vulnerabilities to ensure a robust defense across every layer of your IT environment.

Supply Chain Risk Management
Organizations of all sizes rely on third parties to provide products and services critical to their business functions. This reliance comes with risk: third parties often have access to your systems, networks, and sensitive data. Access Point Consulting helps mitigate these risks by combining comprehensive annual vendor assessments with continuous monitoring of your most critical vendors. You gain complete visibility into your supply chain, protecting your valuable assets from breaches and disruptions.

Penetration Testing
Access Point Consulting’s Penetration Testing service proactively identifies and fortifies vulnerabilities in your infrastructure through realistic attack simulations. We provide clear, actionable insights to strengthen defenses, protect sensitive data, and prevent threats from bypassing conventional security measures.

Brand & Domain Monitoring
Access Point Consulting’s Brand & Domain Monitoring service protects your organization's online identity and reputation. Leveraging external monitoring strategies, we identify and respond to potential threats like impersonation, unauthorized domain use, and brand misuse—preserving customer trust and brand integrity.

Service Packages
Assess, design, and implement your information security program with a curated suite of services, tailor-made to suit your company’s needs.
APC Essentials

Virtual CISO
Strategic security leadership

Endpoint Detection & Response
Monitor and defend

Zero Trust Network Access
Enforce least privilege
Cloud Optimization (add-on)
Improve cloud posture
APC Compliance

Virtual CISO
Strategic security leadership

Supply Chain Risk Management
Secure vendor relationships

Data Protection
Protect sensitive data

Managed Detection & Response
Detect and respond

Zero Trust Network Access
Enforce least privilege
Cloud Optimization (add-on)
Improve cloud posture
Penetration Testing (add-on)
Simulate attack scenarios
APC Security

Virtual CISO
Strategic security leadership

Supply Chain Risk Management
Secure vendor relationships

Brand & Domain Monitoring
Monitor external threats

Zero Trust Network Access
Enforce least privilege

Data Protection
Protect sensitive data

eXtended Detection & Response
Rapid threat response
Cloud Optimization (add-on)
Improve cloud posture
Penetration Testing (add-on)
Simulate attack scenarios
.png)
Working With Us
In order to quickly and efficiently provide value to your organization, our team follows a direct approach to client onboarding. From day one, we operate as a trusted advisor to your team, offering only those solutions most needed by your organization.
Discovery

We begin with a discovery call, where we discuss your specific cybersecurity challenges, goals, and any pressing concerns. This conversation helps us gain insight into your business and security environment, allowing us to tailor our approach right from the start.
Proposal

Based on our initial discovery, we prepare a proposal which outlines our recommended engagement model and pricing. Each proposal includes a high-level project plan and deliverables mapped to your specific objectives. We work closely with you to ensure the proposal aligns with your security needs and organizational priorities.
Service Agreement

Once the proposal is reviewed and accepted, we move to formalize the partnership with a service agreement. This agreement clearly defines the scope of work and terms of service, ensuring transparency at every step. The service agreement acts as a roadmap for the initial engagement, providing clarity on expectations and outcomes.
Kickoff

Once an agreement has been signed, we ensure that our team is fully integrated with your organization's in-house team. Here we introduce key stakeholders and establish communication channels. Our team becomes an extension of your organization, ensuring a seamless engagement from start to finish.
Ongoing Client Support

Our commitment to your success extends well beyond the initial engagement. We build long-term partnerships by providing proactive support throughout every phase of our relationship, ensuring your cybersecurity program remains aligned with evolving risks, regulations, and business needs. Our goal is to anticipate challenges before they arise, offering tailored guidance and hands-on support every step of the way, so you can stay focused on what matters most—driving your business forward with confidence.
Working With Us
In order to quickly and efficiently provide value to your organization, our team follows a direct approach to client onboarding. From day one, we operate as a trusted advisor to your team, offering only those solutions most needed by your organization.
Frequently Asked Questions
Find answers to common questions about our VCISO service.
The vCISO service at Access Point Consulting is designed to complement and strengthen your existing IT and security teams––not replace them. We’ll work with you in a collaborative partnership, ensuring that the information security strategies we develop support and advance your organization's mission and objectives. Rest assured that initiatives that flow from the strategy will fit your goals, risk tolerance, and compliance requirements. Your vCISO will also provide the invaluable service of facilitating effective communication among IT, security, and senior leadership, ensuring that everyone is informed and aligned on security initiatives and strategies.
We’ll provide you full contact information and you’ll have multiple ways to reach your vCISO immediately. If for some reason your vCISO can’t pick up in that moment, you can expect to receive a response within 15 minutes.
Our vCISO service takes a methodical and collaborative approach to defining and implementing security policies. The process begins with an assessment of your organization's current security posture, risk appetite and tolerance. We evaluate your company’s existing policies, practices, security skills, and vulnerabilities. Based on the findings, your vCISO will draft security policies, playbooks, standards, and procedures that will bring your company into compliance. These are thoroughly vetted and approved. We then work with you to make these fully functional policies an integral and essential part of your organization's culture and day-to-day operations. Training sessions and awareness programs are put in place to support the effort. Your vCISO will assist in monitoring and enforcing policy adherence, implementing security controls and technologies to support policy enforcement. Finally, your vCISO will ensure that all security policies are documented in a clear and accessible manner to ensure ongoing compliance and adaptability to evolving security challenges.
Our risk assessments typically cover operational risk, information security and technology risk, compliance and regulatory risk, and strategic and reputational risk. By addressing risks within these categories, your organization is better positioned to manage and mitigate a wide range of potential threats and challenges. Access Point risk assessments are developed in collaboration with a designated resource from your organization who helps us understand your unique risks and can provide information and documentation. You’ll receive from us an honest assessment of your risk landscape and recommendations to resolve any issues discovered. Risk assessments are generally conducted periodically, on an as-needed basis, but we recommend updating your risk assessment quarterly or in response to major changes that affect your business such as mergers, acquisitions, changed industry regulations, and infrastructure buildouts.
We employ a comprehensive approach that includes ongoing monitoring of regulatory changes, regular audits, education and training, policy updates, and proactive risk management strategies. Access Point vCISOs receive a minimum of 40 hours of professional training annually and make it a priority to stay up-to-date on evolving regulations that impact your business. You can count on us to keep you informed of impending compliance challenges and changes in regulations that will affect your business. Our goal is to keep your organization current, reduce compliance risks, and facilitate a culture of compliance.
Access Point vCISOs are experts in the healthcare, financial services, technology, energy, and military sectors.
Our approach leverages a combination of industry-standard cybersecurity toolsets within your organization, third-party technologies, and privately developed toolsets. Your vCISO is supported by an in-house team of more than 100 technology experts who are charged with ensuring the technical accuracy of every assessment and recommendation. Senior technical engineers in their respective fields participate in an in-depth peer review process to validate the material for completeness, clarity, concision, and technical accuracy.
Access Point is committed to client data security. As security and privacy experts, we use state of the art cloud privacy and strong encryption with all data, at rest or in motion. We offer “crypto-shredding” of client data saved to our cloud environments. We will clearly articulate that once data has been crypto-shredded, that is a non-reversible data destruction event. Once data has been crypto-shredded there is no way to reverse the process. It is the final step of an engagement. This is comforting for clients that are concerned about any potential breaches or future breaches. The data is always encrypted and keys are encrypted and destroyed, resulting in unrecoverable encrypted data. Without the key, no one can recover the data, not even your vCISO.
Resources
Latest Resources

September 30, 2025
Insights from this Year's IBM Report
Each year, IBM releases its Cost of a Data Breach Report, one of the most widely cited studies on the financial and operational impact of cyber incidents. The latest edition shows that while costs continue to rise — now averaging $4.88 million globally per breach, with U.S. organizations facing even higher averages — the story is about preparation and discipline. The numbers remind us that breaches are not rare, isolated events. They are part of the operating environment organizations must manage. The question isn’t if an incident will occur, but how ready your team will be when it does.
.jpg)
April 2, 2025
Scott "Monty" Montgomery (Island) | Navigating CMMC compliance for organizations of every size
Scott Montgomery, known as Monty, joined the CyberWatch Expert Series podcast to discuss his extensive background in cybersecurity, particularly in building and designing network security tools for high-assurance environments like the Department of Defense (DoD) and the intelligence community. His experience includes significant tenure at McAfee (now Trellix), which led him to his current role at Island, where he focuses on innovative approaches to cybersecurity compliance.
September 25, 2025
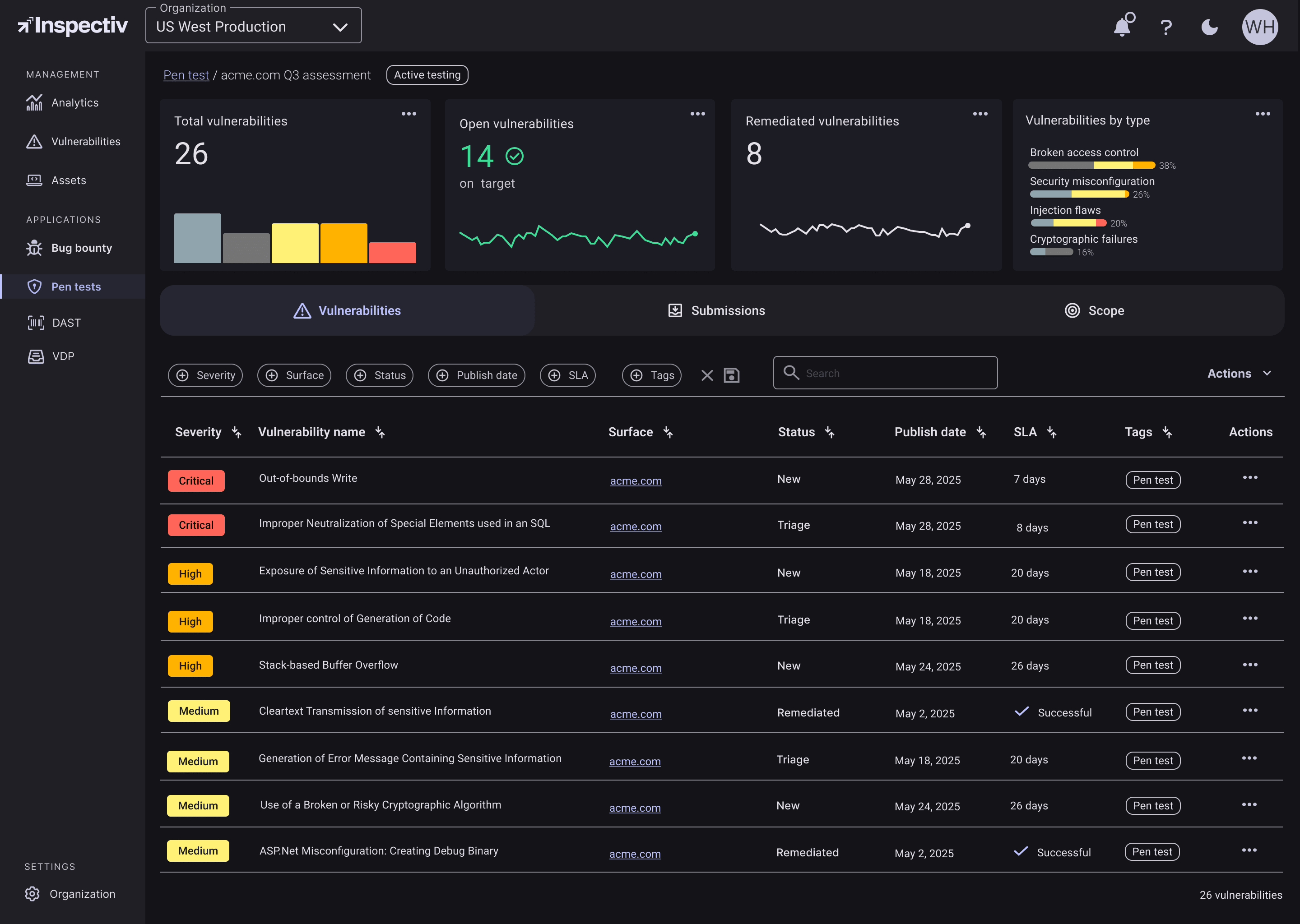
Access Point Consulting announces partnership with Inspectiv to deliver stronger, faster application security for scaling organizations
Access Point Consulting today announced a strategic partnership with Inspectiv, a leader in application security testing whose platform unifies bug bounty programs, methodology-driven penetration testing, continuous DAST scanning, and vulnerability disclosure programs. The partnership enables Access Point customers to find real vulnerabilities faster and translate findings into validated, prioritized remediation—with 365-day free retesting to confirm fixes.


